Penetration Testing vs. Vulnerability Scanning. I am often amazed at how a vulnerability scan is sold as a penetration test. On more than one occasion, I have


Penetration definition, the act or power of penetrating. See more.



Overview. The aim of this section of the PTES is to present and explain the tools and techniques available which aid in a successful pre-engagement step of a
Discover what is a vulnerability assessment and penetration testing (VAPT) and how Veracode’s platform help you reduce application security risks.
This network penetration testing guide reveals how to use penetration testing tools and best practices for conducting a penetration test.
Learn the methodology and tools of network penetration testing through practical, applicable course content and hands-on labs in our core pen testing course.
Penetration testing aka Pen Test is the most commonly used security testing technique for web applications. This is your web application penetration testing getting
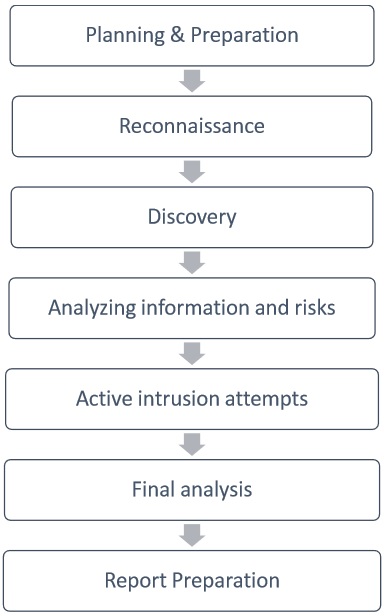

High Level Organization of the Standard. The penetration testing execution standard consists of seven (7) main sections. These cover everything related to a
List of penetration testing tip sheets courtesy of SANS: pdfs, downloads and more.
Penetration testing (also known as intrusion detection and red teaming) is security-oriented probing of a computer system or network to seek out vulnerabilities that
